|
As mobile apps occupy a growing proportion of the time people spend using computers and digital services, being able to easily link to content inside mobile apps could make them easier to use and also boost the mobile ad industry. Deep links will have a much broader impact than just boosting ads, by bringing some of the openness of the Web to the world of apps. -By Philippe Mora
[Thank You MIT Technology Review | By Tom Simonite 02.04.14] In the beginning there was the Web, a thicket of virtual pages connected by hyperlinks that enabled blogging to flourish and companies like Google to make piles of money by directing people where advertisers wanted them to go. Today mobile apps increasingly rule our free time and require us to dive into separate, walled-off digital containers that don’t link up. That’s now changing as ad technology startups, together with established companies such as Google and Facebook, seek to reinvent the hyperlink. They’re rolling out technology that makes it easy to put links into a mobile app, Web page, or e-mail that with a single tap take a person to a specific section of another app installed on the device. “This should be a fundamental building block of how all mobile apps work, just like URLs are fundamental to how the Web works,” says Sriram Krishnan, a product manager at Facebook. The new kind of hyperlink could make apps seem less walled off from one another. Deep linking, as the technology is called, is also seen as a way to open up new forms of advertising that will provide revenue to make mobile advertising more closely match its online counterpart (see “Why No One Likes Mobile Ads”). Support for deep linking has been built into Apple and Google’s mobile operating systems for some time. It allows app developers to give URL-like identifiers such as “iOSApp://location/123456” to specific sections within an app. However, uptake by mobile app developers was initially slow due to differences in how the feature worked on different operating systems and a lack of broad support for their usage. Technology companies large and small are now driving wider adoption of deep linking by offering technology that makes it easy to deploy, manage, and use deep links. Twitter and Facebook are perhaps the most influential companies pushing for deep links to be used more widely. Last April, Twitter added support for deep links in the “cards” that companies can use to display rich media alongside Twitter messages sent from their website or app. The support was also added to “promoted,” or paid for, tweets. Facebook had already, in 2012, allowed deep links to appear in posts to its News Feed, but last October the company began selling a new kind of mobile ad based on deep linking. They allow companies to show people ads based on their Facebook likes that take them directly to a specific place inside a mobile app.
0 Comments
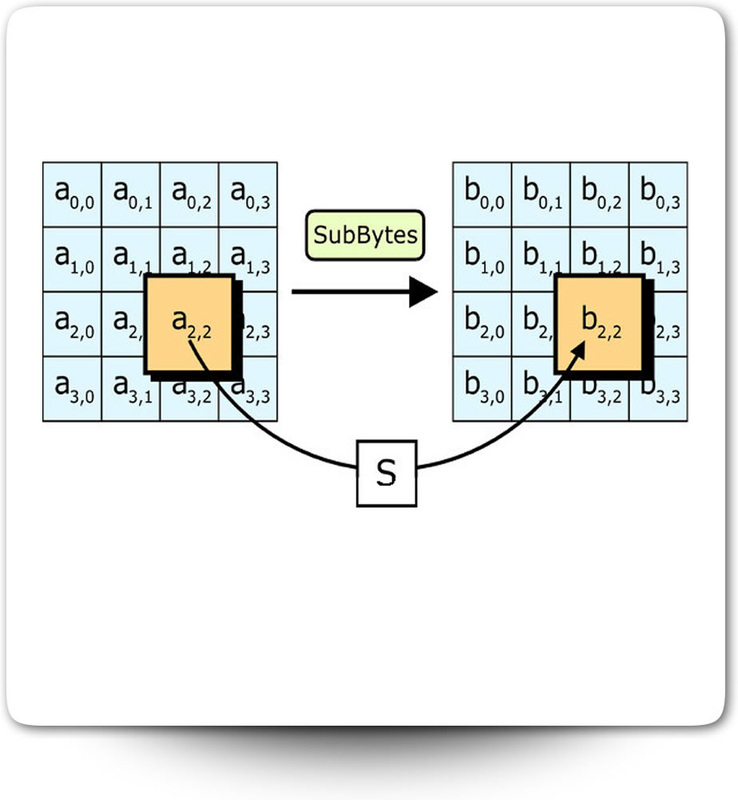
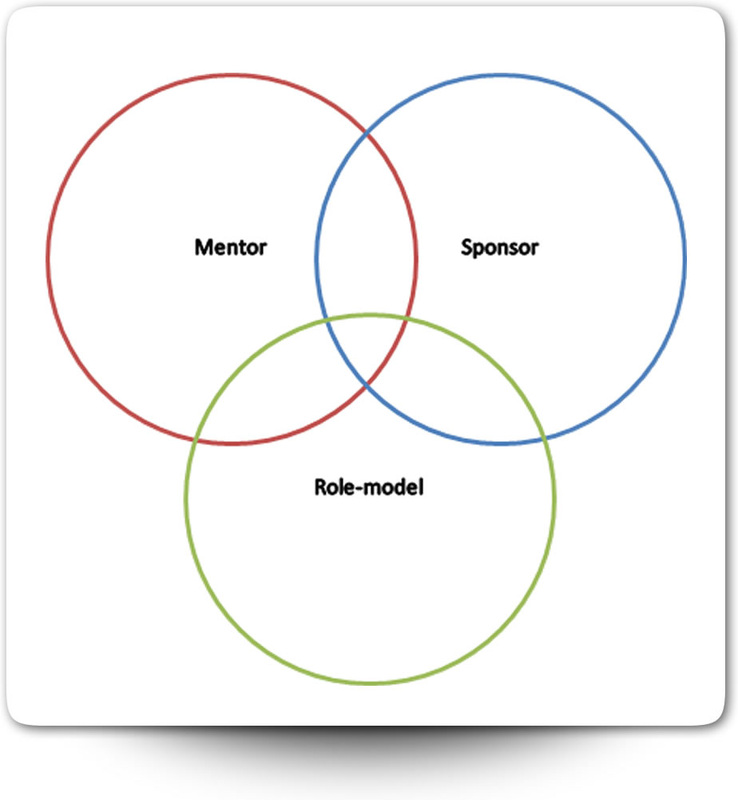
Encrypted data often leaks online and criminals have proved capable of decrypting it. A new approach to encryption beats attackers by presenting them with fake data: creating a fake password vault generator needed for Honey Encryption will protect password managers -By Philippe Mora [Thank You MIT Technology Review | By Tom Simonite 01.29.14] Ari Juels, an independent researcher who was previously chief scientist at computer security company RSA, thinks something important is missing from the cryptography protecting our sensitive data: trickery. “Decoys and deception are really underexploited tools in fundamental computer security,” Juels says. Together with Thomas Ristenpart of the University of Wisconsin, he has developed a new encryption system with a devious streak. It gives encrypted data an additional layer of protection by serving up fake data in response to every incorrect guess of the password or encryption key. If the attacker does eventually guess correctly, the real data should be lost amongst the crowd of spoof data. The new approach could be valuable given how frequently large encrypted stashes of sensitive data fall into the hands of criminals. Some 150 million usernames and passwords were taken from Adobe servers in October 2013, for example. After capturing encrypted data, criminals often use software to repeatedly guess the password or cryptographic key used to protect it. The design of conventional cryptographic systems makes it easy to know when such a guess is correct or not: the wrong key produces a garbled mess, not a recognizable piece of raw data. Juels and Ristenpart’s approach, known as Honey Encryption, makes it harder for an attacker to know if they have guessed a password or encryption key correctly or not. When the wrong key is used to decrypt something protected by their system, the Honey Encryption software generates a piece of fake data resembling the true data. If an attacker used software to make 10,000 attempts to decrypt a credit card number, for example, they would get back 10,000 different fake credit card numbers. “Each decryption is going to look plausible,” says Juels. “The attacker has no way to distinguish a priori which is correct.” Juels previously worked with Ron Rivest, the “R” in RSA, to develop a system called Honey Words to protect password databases by also stuffing them with false passwords. Juels and Ristenpart will present a paper on Honey Encryption at the Eurocryptcryptography conference later this year. Juels is also working on building a system based on it to protect the data stored by password manager services such as LastPass and Dashlane. These services store all of a person’s different passwords in an encrypted form, protected by a single master password, so that software can automatically enter them into websites. Password managers are a tasty target for criminals, says Juels. He believes that many people use an insecure master password to protect their collection. “The way they’re constructed discourages the use of a strong password because you’re constantly having to type it in—also on a mobile device in many cases.” Juels predicts that if criminals got hold of a large collection of encrypted password vaults they could probably unlock many of them without too much trouble by guessing at the master passwords. But if those vaults were protected with Honey Encryption, each incorrect attempt to decrypt a vault would yield a fake one instead. Hristo Bojinov, CEO and founder of mobile software company Anfacto, who has previously worked on the problem of protecting password vaults as a security researcher, says Honey Encryption could help reduce their vulnerability. But he notes that not every type of data will be easy to protect this way since it’s not always possible to know the encrypted data in enough detail to produce believable fakes. “Not all authentication or encryption systems yield themselves to being ‘honeyed.’” Juels agrees, but is convinced that by now enough password dumps have leaked online to make it possible to create fakes that accurately mimic collections of real passwords. He is currently working on creating the fake password vault generator needed for Honey Encryption to be used to protect password managers. This generator will draw on data from a small collection of leaked password manager vaults, several large collections of leaked passwords, and a model of real-world password use built into a powerful password [Read More: http://www.technologyreview.com/news/523746/honey-encryption-will-bamboozle-attackers-with-fake-secrets/] Finding the right person to highlight your accomplishments and push you to the top is a hard task, but it’s necessary if you want to break out of the “permanent lieutenant” doldrums. Just doing good work isn’t enough. Take the first step and make yourself not only a hard worker, but an emerging leader worthy of a sponsor. -By Philippe Mora
[Thank You HBR | By Ann Hewlett | 02.06.14] “I’ve always given 110%,” says Maggie. “Whoever I worked for, I gave them my all, every day, 10 hours a day, weekends and holidays, whatever it took. That endeared me to a lot of powerful men.” That dedication and loyalty should have made Maggie a star. Yet, although she rose in the organization, because she wasn’t strategic about whom she gave her 110% to, she squandered her gifts on leaders who didn’t invest in her. Without a sponsor to spotlight her attributes, offer her opportunities, and kick her career into high gear for years, she found herself stuck in what she calls “permanent lieutenant syndrome.” Maggie eventually was fortunate enough to find a sponsor and today is an executive at a global financial advisory firm with 22,000 people reporting to her. But there are thousands of Maggies out there — hardworking, devoted, consistent performers toiling in relative obscurity. How can you break out of the pack and attract a sponsor? Rather than hoping for a lucky break, focus your energies by making yourself sponsor-worthy. To begin with, you must come through on two obvious fronts: performance and loyalty. When asked how she had built great relationships with three different sponsors, Sian McIntyre, head of Legal at Lloyd’s Banking Group, says simply, “I’ve delivered.” She hit her targets and deadlines, executed brilliantly on her assignments, and produced outstanding bottom-line results. “They all felt the benefit of that,” McIntyre notes, “and wanted me on board for subsequent projects.” Loyalty manifests in many different ways: trust that’s earned through repeated demonstration of a dedicated work ethic, commitment to a shared mission, and allegiance to the firm. Winning a sponsor’s trust doesn’t require becoming a toady. On the contrary, showing that you can ultimately be entrusted with a leadership position depends on demonstrating that you will stand up to him or her when necessary. Tiger Tyagarajan, CEO of Genpact, attributes his success to the bond he cultivated with Pramod Bhasin, his boss and sponsor for 17 years. Because of a deep trust built on shared values, Bhasin would listen when Tiger pushed back. “I’d say, ‘Here’s my logic on this,’ and show him that I understood his logic but also show him why it wouldn’t work. He was amenable to that as long as I kept it private,” Tiger recalls. “We had very different styles, and sometimes we simply agreed to disagree. But in the end, I think that what he valued in me was the very thing that complemented him.” But performance and loyalty are not enough to get a sponsor’s notice, let alone convince him to invest in you. You’ll need to differentiate yourself from your peers. You’ll need to develop and deploy a personal brand. You’ll need to do something or be someone who can extend a sponsor’s reach and influence by adding distinct value. What do you bring to the table? Some protégés add value through their technical expertise or social media savvy. Others derive an enduring identity through fluency in another language or culture. Consider acquiring skills that your job doesn’t require but which set you apart — and make you a stronger contributor to a team. For example, Tiger Tyagarajan had a special ability to build teams from scratch and coach raw talent — an invaluable asset that was key as the firm transitioned from a start-up into a multinational info-tech giant. One 25-year-old sales rep, noting her potential sponsor “wasn’t exactly current in terms of the internet,” took pains to brief her on job candidates whose resumes bristled with technical jargon and references to social media innovation that she simply couldn’t understand, let along assess for relevance. “I just helped educate her so she didn’t come off as some kind of dinosaur,” says the rep, whose tactful teaching gained her a powerful promoter. Lastly, don’t be shy about your successes. Alert potential sponsors to your valuable assets. Since it can be difficult to toot your own horn, work with peers to sing each other’s praises. A VP at Merrill Lynch described how she and three other women, all high-potential leaders in different divisions of the firm, would meet monthly for lunch to update each other on their projects and accomplishments. The idea was to be ready to talk each other up, should an occasion arise. “So if my boss were to complain about some problem he’s struggling to solve, I could say, ‘You know, you should talk to Lisa in global equities, because she’s had a lot of experience with that,’” this VP explained. “It turned out to be a really effective tactic, because we could be quite compelling about each other’s accomplishments.” In short order, all four women acquired sponsors and were promoted. Finding the right person to highlight your accomplishments and push you to the top is a hard task, but it’s necessary if you want to break out of the “permanent lieutenant” doldrums. Just doing good work isn’t enough. Take the first step and make yourself not only a hard worker, but an emerging leader worthy of a sponsor. [Read More: http://blogs.hbr.org/2014/02/make-yourself-sponsor-worthy/] SYLVIA ANN HEWLETT Sylvia Ann Hewlett is Chairman and CEO of the Center for Talent Innovation. She is the author of 10 books, including Forget a Mentor, Find a Sponsor. Follow her on Twitter at@sahewlett. Twitter’s first earnings report shows that growth is slowing. Could it be a sign it’s meant to be a niche network?
As Twitter ages, it will have to try new tactics if it wants to keep adding new users. -Philippe [Thank You MIT Technology Review | By Rachel Metz on 02.06.14] After Twitter’s first quarterly report as a publicly traded company indicated slowing growth, the company is facing some skepticism about its prospects as a mainstream social network. Late Wednesday, the company issued its fourth-quarter results, showing that the number of active monthly users totaled 241 million at the end of December—a jump of 30 percent year over year, but up just 4 percent from the quarter that ended in September and a smaller increase than it showed in that period. Meanwhile, the number of times users looked at their feeds of tweets on the site climbed 26 percent to 148 billion when compared with the same quarter a year earlier, but fell 7 percent from the prior quarter. Several analysts issued concerned reactions to the report, such as Sterne Agee analyst Arvind Bhatia, who said in a client note that the results “are likely to raise questions on how mainstream the Twitter platform can be in the long term.” Investors drove the stock down 24 percent, or $15.94, in trading to close the day at $50.03 (the stock has traded as high as $74.73 since the company went public in November). The issue, in part, seems to be that for Twitter to keep growing, it needs to figure out how to appeal to more types of users, and make it easier for them to use the service. It is popular with a number of groups, such as journalists, celebrities (and their followers), and news junkies. But since it’s not as clearly focused as Facebook is on connecting with friends and family, it may be harder for it to gain such broad appeal. During a call with financial analysts to discuss the quarterly results, CEO Dick Costolo said Twitter is trying to grow by making content—tweets, photos, and videos—the main focus, rather than the “scaffolding of the language of Twitter.” Recent changes to make this happen include featuring photos and videos right on users’ main Twitter feeds, and making a direct-messaging feature more prominent in some of Twitter’s mobile apps. The changes appear to be helping current users engage more with the service, at least. Since the new features were rolled out during the fourth quarter, users are increasingly “favoriting” and retweeting others’ tweets, Costolo said. But there’s clearly more work to be done if the company wants to remain what Costolo calls “the best product in the world for real-time, in-the-moment interaction, conversation, and discovery.” Twitter is working on a number of things, Costolo said, as he mentioned efforts to make it easier to sign up for the service and bring back currently inactive users. Colin Sebastian, an analyst at Robert W. Baird & Co., thinks one way Twitter could get the average user more interested is through more real-time search features that make it easy to find, say, updates on the latest food or entertainment in San Francisco. That would make sense, considering Costolo said searches on the site more than doubled year over year in the October-December period. Sebastian suggests it could benefit from taking a look at how Facebook heavily curates users’ news feeds on its site. Doing something similar on Twitter could help make the service less overwhelming for new users, he says. [Read More: http://www.technologyreview.com/news/524426/it-turns-out-twitters-not-for-everyone/] |
head of product in colorado. travel 🚀 work 🌵 food 🍔 rocky mountains, tech and dogs 🐾Categories
All
|









 RSS Feed
RSS Feed